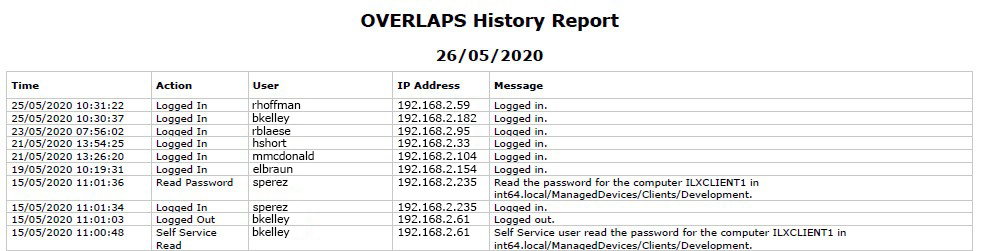
Installing the OVERLAPS Trial – Step-by-step
Introduction This article is a (very) quick look at the process we regularly follow to setup a test instance of OVERLAPS. Its intended purpose is to show the broad steps to demonstrate how easy it is to install a baseline configuration and get your initial instance of OVERLAPS up and running. Note that some settings…
 Int64 Software Ltd
Int64 Software Ltd