23. Settings
The Settings page provide access to the OVERLAPS main configuration options.
23.1 Security
23.1.1 Organizational Unit Visibility
By default, if a user does not have permission to access a container above the current container, it will still appear in the breadcrumbs on the computer list screen so that users are given a more complete view of the Active Directory structure. Any containers for which they do not have access cannot be clicked on, they are simply there for reference, as shown below.

However, by checking the Hide Organizational Units that a user doesn’t have permission to access box these containers will no longer appear in the breadcrumbs, instead only the containers that the user has permission to read will be shown.
23.1.2 Notifications Require "View History" Permission
If unchecked, any user with permission to read computer passwords (with or without authorisation) can set up notifications for events occuring in a container (such as other users reading a computer's password). By checking this box, they will only be allowed to do this if they also have permission to view the History page.
23.1.3 Authorisation Requests
23.1.3.1 Authorisation Request Expiry
By default, requests to view a computer’s password which have been authorised will expire 24 hours (1440 minutes) after the password is viewed by the Requestor. This means that if the Requestor attempts to view the password again after this time has passed they will need to submit another request.
This grace period can be removed by changing this value to "0" which will cause the request to expire immediately when the user views the password, meaning that any subsequent attempts will require a new Authorisation Request.
This does not prevent a user from keeping the view password window open but will stop them from re-opening it once the expiry period has passed.
23.1.3.2 Authorisation Request Maximum Age
Change this value (shown in minutes) to specify how long Authorisation Requests are kept before they are automatically cleaned up (deleted). This defaults to 1440 minutes (24 hours).
Authorisation Requests older than this will be deleted regardless of their status.
23.1.3.3 Send a copy of all Authorisation Requests to this email address
By default, when a user submits an Authorisation Request to view or expire a computer's password, the request is emailed to all users marked as an Authorisor for that container. This option allows you to also send a copy of the request to another email address, such as a shared mailbox.
You can combine this with the Do not email Authorisers individually checkbox to only use this address to send requests to.
23.1.3.4 Do not email Authorisers individually
If checked, users with the permission to authorize requests will not be emailed when a request is made. This can be used in combination with the above setting to use a shared mailbox for request authorization.
23.1.3.5 Prevent Authorisers from Authorising their own Requests
Setting this option makes it so that nominated Authorisers cannot authorise their own Authorisation Requests and must get someone else to allow or deny it.
23.1.3.6 Authorisation Request Email Format
Select whether Authorisation Request emails are formatted as a Summary (the number of pending requests that the recipient has outstanding), or Detailed (which includes a full list of requests).
23.1.4 Two Factor Authentication Settings
23.1.4.1 OVERLAPS Identification for Authenticator Apps
By default, when a user enables Two Factor Authentication (2FA), OVERLAPS will identify itself in their Authenticator app as “OVERLAPS”. However, if you are running more than one OVERLAPS server, this can become confusing.
Changing this setting allows you to specify a custom identifier that will be used whenever a user enables 2FA. Note that this only works when using the QR code to register OVERLAPS in an authenticator app as the manual code allows users to enter any text as the identifier.
23.1.4.2 Enforce Two Factor Authentication for All Users
If this option is checked, the next time any user without 2FA enabled logs in they will be prompted to enable it and given a QR Code to enter into their Authenticator app. Once done, they will then be required to enter a code from that app before they can complete the login.
23.1.4.3 Maximum Days to Remember Devices
Set how long (in days) a device will be remembered when the user selected the "Remember this Device" option when completing a 2FA login. Once this period has expired the user will be required to enter a 2FA code again. This is 30 days by default, and can be set to any value between 1 and 90 days.
23.1.4.4 Recommended Authenticator Apps
Enable or disable which TOTP authenticator apps are suggested to users when they go to enable Two Factor Authentication.
23.1.4.5 Custom Authenticator App
If the Authenticator app used by your company is not shown in the list above you can add it yourself by supply its name, and a link to where it can be downloaded on either the Apple App Store and/or the Google Play Store.
If you want this included in the main list instead, just email us the details to support@int64software.com and we will check to make sure it is appropriate and add it to the list if approved.
23.1.5 Login Settings
23.1.5.1 Default Login Domain
If you have multiple domains and would like a particular one to be selected by default on the login screen, select it here.
23.1.5.2 Display the standard login form on the login screen.
If you are prioritising Windows Authentication (WIA) or SAML authentication, then this provides the option to hide the form login from the login screen. However, if neither WIA or SAML are enabled then this setting will be ignored and the form will show so that users can still login.
23.1.5.3 Display the "Login using Windows Authentication" button on the login screen
Checking this box hides the button on the login screen for logging in with Windows Integrated Authentication (WIA).
23.1.6 SAML
Configuration options for Security Assertion Markup Language (SAML). See here for full details.
23.2 Password Reset Options
23.2.1 Automatic Password Reset
By default, LAPS will automatically reset your passwords based on the schedule defined in Group Policy. Instead of waiting for this, you can use these settings to automatically expire passwords after a certain amount of time has passed from when they were last accessed.
There are two values to set: one for the normal accessing of passwords through the Computer Browser, and one for users who access passwords through Self Service.
Note that this will set the passwords to expire after the given amount of time from when they are accessed, but passwords are only actually reset on a Group Policy update on the computer itself.
If you use the new Windows LAPS "Post-authentication actions" group policy for managing this, then you can safely leave this disabled by setting both values to "0".
23.2.2 Allow All Users to Specify an Expiry Date and Time
If enabled, when expiring a computer’s LAPS-managed password, all users will be able to specify a date and time that the password should expire (instead of immediately).
23.2.3 Maximum Expiry Period
Specifies how many days in the future that a password can be set to expire. This should not be more than your Group Policy setting for LAPS password age.
23.3 Logging and History
23.3.1 Log Level
Specifies what level of information is saved to the OVERLAPS log file. This is Information by default but can be increased to Verbose when debugging is required or lowered to keep the size of the log file down.
This can also be set to the absolute highest level of Debug when an extra level of detail is required, but as this outputs a lot of data it should only be enabled for short periods of time when needed.
Note that the log level is automatically increased to Verbose for one week after any new installation or upgrade to aid our Support Team in case of any installation issues that may arise. You can override this behaviour by deleting the ".init" file from "C:\ProgramData\Int64 Software Ltd\OVERLAPS\".
23.3.2 Delete History Data Older Than This
The amount of time to keep data in the History log before it is deleted. You can customise this depending on your space limitations, amount of activity, and Data Protection laws. The valid values are anywhere from a single day up to 5 years.
23.3.3 Windows Event Log
To improve support for Security Information and Event Management (SIEM) products, you can check individual event types in this section to have them automatically written to the server’s Windows Event Log as well as OVERLAPS’ own history log. These can then be more easily captured or monitored for security alerts and auditing purposes.
Simply check the box for each event you want to have added to the Event Log or use the Select All/None links to enable/disable all events being sent to the Event Log.
23.3.4 Password History
Occasionally the need arises to see what a computer's password used to be, such as when System Restore is used and the password in AD is no longer correct. Enabling this option (by setting its value to more than 0) tells OVERLAPS that you would like it to store a copy of the passwords so that you can look back using the Password History tab and page.
If enabled, OVERLAPS scans Active Directory each night for computers that have changed. It then retrieves their passwords, encrypts them, and writes them to its database for access later.
23.4 Active Directory
23.4.1 Active Directory Structure
23.4.1.1 Active Directory Structure Update Frequency
Change this to modify how often OVERLAPS performs a full scan of Active Directory for changes to its structure. Changes it looks for include: new Organisational Units (OUs), removed OUs, and moved or renamed OUs.
Finding the correct values for this will depend on many things including the overall size of your domain, and how frequently it changes.
Note that this only covers the full scan and refresh of the AD structure. In addition to this, OVERLAPS runs a smaller scan for specific changes every 30 minutes.
By default this is set to "Every day (during the night only)".
23.4.1.2 Automatically Scan On Service Start
Check this box to have OVERLAPS automatically carry out a full Active Directory structure scan whenever the service reloads. This is not usually needed but can be used in combination with the Update Frequency to more accurately control when a scan takes place.
23.4.1.3 Schedule Scan Now
Check this box to request an Active Directory structure scan at the next available opportunity (usually within a few minutes).
23.4.2 Active Directory Groups Refresh
23.4.2.1 Group Refresh Frequency
To decrease overhead on the login process, OVERLAPS periodically scans any groups that have been added for new users or users that have been removed. Set this value to control how often this happens.
**Note that this is not required for new group members logging in the first time, but is more important for preventing users who have been removed from a group from logging in. **
23.4.2.2 Queue Group Refresh Operations
If checked, group refresh triggers are added to a queue and processed sequentially. Otherwise the operations are handled in a multithreaded manner.
23.4.3 Active Directory Domains
Here you will see a list of all domains that OVERLAPS has detected in your forest, and any forests with which you have a trust relationship. Each domain can be enabled or disabled for use or access within OVERLAPS.
Note that the current root domain cannot be disabled.
23.4.3.1 Active Directory Credentials
By default, the OVERLAPS server’s LOCAL SYSTEM account is used to query Active Directory. However, in environments where this is not practical, you can provide the credentials of an alternate Service Account here. OVERLAPS will then use this account when retrieving any information from Active Directory.
**Note that these credentials are stored encrypted in the OVERLAPS database. **
23.4.3.2 Directory Connection Priority
In order to provide the maximum the level of support for all possible Active Directory configurations, OVERLAPS supports all three principal means of querying it:
Directory Searchers
Lightweight Directory Access Protocol (LDAP)
Security Principals
By default, OVERLAPS will prefer the Directory Searchers protocol. However, if you are having domain connectivity issues then you can try the others for User, Group and Computer operations as best suit your environment.
Generally speaking, these should be left as the defaults unless you are experiencing problems when adding users or getting the members of groups. If you have any doubts, please contact our Support Team for assistance (Getting Support).
23.4.4 Permissions Snapshot Settings
Permissions snapshots are used to capture the state of your container permissions prior to making any changes so that the permissions can be restored if something goes wrong.
23.4.4.1 Snapshot Container Names
If checked, along with the permissions, the snapshot will also record the new names of any renamed containers.
23.4.4.2 Fully Revert Container Names
If the above has been checked as well, when restoring a snapshot it will fully replace all container names with those from the snapshot. If the snapshot does not contain a new name for a container, but that container has subsequently been renamed, then it will revert it back to the default. Leaving this unchecked means that this latter situation will retain the new name.
23.4.4.3 Scheduled Snapshots
If checked, a snapshot of your permissions is automatically capture every night.
23.4.4.4 Remove automatic snapshots once they are old than this many days
Specify how long to keep automatic snapshots if they are enabled above.
23.4.5 Domain Controller Settings
23.4.5.1 Enable Domain Controller Caching
By default, OVERLAPS will scan your network for Domain Controllers and maintain an internal cache of them so it knows which ones to use. However, if you regularly have DCs going offline, this can lead to errors where OVERLAPS doesn't realise this and continues trying to query it. For this reason you can uncheck this box to make OVERLAPS stop using its cache and instead request a DC from AD for each request.
23.4.5.2 Domain Controller Health Check
If enabled, OVERLAPS will periodically scan known Domain Controllers to make sure it can talk to them. If it can't then the DC is automatically blacklisted so that no further attempts are made to use it. This can be used as an alternative to disabling the Cache, but generally shouldn't be required.
23.4.6 Workarounds
This section is provided for current and future workarounds we may deploy to resolve issues in very specific domain environments. These options should generally only be modified if you encounter an issue that you feel may be related, or if you want to try out one of the experimental features. If you have any doubts, or would like to know more about a specific setting, please contact our Support Team (Getting Support).
23.4.6.1 Enable Multi-Forest Authentication
For environments with more than one Active Directory forest and the need for users of different (trusted) forests to login to OVERLAPS. Enabling this feature will allow you to add groups and users from the other forests in your network.
23.4.6.2 Measure Query Performance
If checked, most Active Directory operations will be measured to help locate bottlenecks. This information is only written to the log, and only if the Log Level is set to Debug. Note that enabling this feature may also impact the performance of your OVERLAPS server.
23.4.6.3 Allow users with the Read Computer Information permission to access Bitlocker Recovery Keys
If checked, any users who have the "Read Computer Information" permission to a container will also be able to retrieve a computer's Bitlocker Recovery Key from the Computer Information window.
This requires additional Active Directory permissions for the OVERLAPS service. For more information on the permissions and how to set them, see Installation and Configuration -> Active Directory -> Bitlocker Recovery Key Permissions.
23.4.6.4 Default Search Container
Sets the default container that the Search window will be set to use when looking up computers (this container and any children beneath it). Note that users can override this setting when performing a search.
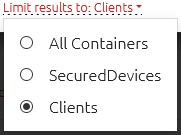
Click Browse to show a tree for you to select a container from. Clicking Clear Setting removes this default.
23.5 Microsoft Entra
For instructions on setting up Microsoft Entra support for cloud devices, please see Setting up Microsoft Entra integration.
23.6 Customisation
23.6.1 Branding
This section allows you to modify the branding text in the main menu.
23.6.2 Password Display Options
23.6.2.1 Password Phonetic Alphabet
The View Password window in OVERLAPS supports showing the password using a Phonetic Alphabet (e.g. Alpha, Bravo, etc.). We have provided a series of standard phonetic alphabets to choose between here.
The Phonetic Alphabet information is loaded from text files located in:
C:\Program Files (x86)\OVERLAPS\Lang\PasswordAlphabets
You can modify these or create your own in any plain text editor. The format required is:
- One character per line.
- First enter the character to be replaced, then a tab character, and then the phonetic alternative to replace the character with.
- The case of the letter is shown by changing the case of the phonetic replacement, so only lowercase values are permitted (everything is converted to lowercase on load).
- Some punctuation is allowed, but to avoid display errors some characters may be removed or encoded.
For example:
a alpha
b beta
...
23.6.2.2 Use Large Password Dialog
If you have configured LAPS to generate particularly long random passwords (27 characters or more), the password view dialog may require users to scroll to see the full password. Checking this box will tell OVERLAPS to use a wider window on displays that support it so that the full password can be viewed.
23.6.3 System Language
You can use this to modify the default system language used by OVERLAPS. This will act as the default language in cases where a user has not selected a language in their profile, and where their web browser does not suggest a valid language code to use.
23.6.4 Date and TIme Settings
23.6.4.1 Date Format
Change this to your preferred local date format.
If the format you prefer is not found in the list, it can be customised using standard Date format notation in the Configuration Utility’s Settings tab (remember to reload the OVERLAPS service after modifying it).
23.6.4.2 Use Local Time (Server Time)
By default, OVERLAPS will use the local time zone of the server it is installed on when displaying times. However, if you operate across multiple time zones and would prefer to use UTC then simply uncheck this box.
23.7 Computer Management
23.7.1 Management Thread Settings
Allows you to configure the Computer Management worker to match the performance of your server. If you notice many Computer Management tasks backing up, you can try increasing this to process them faster if your server has sufficient resources.
23.7.2 Use the Local Administrator Account When Possible
If checked, when tasked with performing a Computer Management operation OVERLAPS will attempt to read each computer's Local Admin password from AD first, and if successful it will then use this account to connect to the computer and perform the operation. This can make configuring the permissions for Computer Management tasks easier.
If you have renamed or use a different account for the Local Administrator account, you can also specify this here.
23.7.3 Computer Management Tools
This globally enables or disables the different Computer Management Task tools. Permission must be granted to use the tools on a per-container basis from the Permissions screen.
23.7.4 Scheduled Device Status Email Reports
Use these settings to schedule an automatic report to be run and emailed according to your needs.
23.7.4.1 Report Top Level OU Distinguished Name
The top-level OU to report on. All child OUs will be included in the report.
23.7.4.2 Report Email Sending Frequency (in minutes)
How often (in minutes) the report should be sent. For example, to send the report once a day, set this to 1440 minutes (60 minutes x 24 hours).
23.7.4.3 Report Selection
Which reports should be run on this schedule and emailed.
23.7.4.4 Email Address(es) to Send Reports To
The email address or addresses (semi-colon-separated) to which the report should be sent.
23.7.4.5 Maximum Number of Devices to Include in a Single Report
To prevent very large reports being sent, you can limit the number of devices included in a single report. If the number of devices exceeds this value, you can view the full report via the Reports page.